Shadow IT: the hidden side of your internal infrastructure
What is Shadow IT?
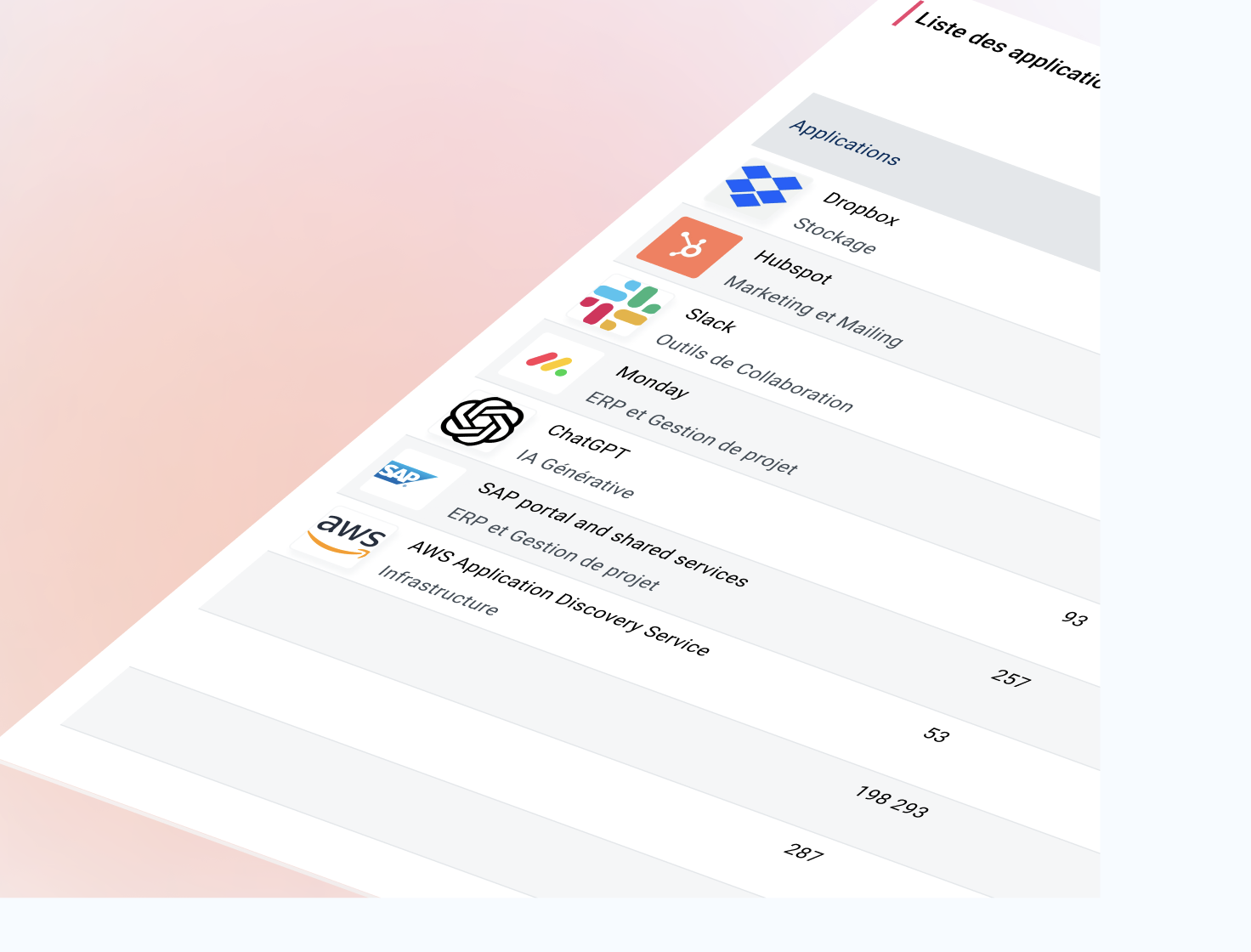
The Shadow IT involves the use of IT tools, software, or applications that are not visible to and are not controlled by the IT department. This has become common practice, since according to Gartner More than 40% of employees use them in the workplace; this includes systems, devices, software, SaaS applications, and other services used by employees but not explicitly authorized by the company or the employer’s IT policy.
These tools are often adopted by employees for legitimate productivity reasons. However, their use poses security and compliance risks because they are outside the control of IT teams. With the rise of cloud services in recent years, shadow IT has become widely available, making it even more difficult for CIOs to control the company's IT infrastructure.
The limits of shadow IT
With the advent of the cloud, employees have become accustomed to easily accessing online applications and tools whenever they feel the need, sometimes without going through the company's approval processes. This can include collaboration tools, data storage tools, or even artificial intelligence (AI) software used to optimize certain professional tasks.
While this autonomy appears to offer benefits in terms of productivity, it also carries numerous risks. From the perspective of CIOs, shadow IT represents a gateway for cyberattacks, data leaks, and compliance violations. Furthermore, it becomes more difficult for the company to ensure data protection and guarantee that the tools used comply with regulatory requirements, such as the GDPR.
Another aggravating factor is the use of personal devices in a professional context, a practice known as BYOD (Bring Your Own Device). These devices, which are often poorly secured, are beyond the control of the IT department and represent additional vulnerabilities in the organization's security.
Furthermore, shadow IT opens the door to a lack of visibility on budgets, with software used by employees that may duplicate solutions already in place within the company. Finally, this unapproved software can lead to vulnerabilities that will inevitably result in additional costs for the company. What's more, if the company were to suffer the loss of confidential or vital data, this could impact its revenue.
The challenges facing CIOs in 2024:
Although shadow IT presents risks, its advantages should not be overlooked. potential benefitsEmployees seek to meet specific needs that are not always addressed by internal tools. It presents opportunities in terms of productivity and innovation, by enabling employees to adopt tools that improve their efficiency, in particular. For example, a marketing department may adopt a SaaS application to collaborate in real time, or a customer service department may use AI to quickly analyze customer data.
However, the mission of CIOs in 2024 is to strike a balance between employee productivity and corporate security. This means enabling employees to work efficiently, while ensuring:
Security vulnerabilities
The use of unapproved solutions creates vulnerabilities that cybercriminals can exploit. Without adequate monitoring, cloud or SaaS applications can introduce vulnerabilities into the corporate network, increasing the risk of malicious attacks. The use of unauthorized services can also lead to the risk of passwords being reused from one application to another, which in the event of a data leak will represent an additional threat.
Compliance and regulations
The use of certain unapproved applications and software may lead to risks of non-compliance with regulations such as the GDPR. This is the case, for example, if sensitive data is stored or shared via non-compliant services, which would expose the company to financial penalties or damage to its reputation.
Lack of control over IT assets
When employees adopt solutions outside the supervision of the IT department, companies lose control over their IT infrastructures, making themanagement and security of these environments more complex.
Raising awareness and educating employees about the risks of shadow IT
It is important to note that in most cases, employees are unaware of the risk they pose to their company. That is why the awareness and the training Regular team meetings are crucial for creating a culture of IT security.
CIOs must implement training programs to explain the dangers of using unapproved applications and the best practices to follow.
Budget management
When a large number of unauthorized tools are used, CIOs lose visibility into software and service expenses. This can lead to wasted resources, with duplicate SaaS subscriptions or unexpected management and security costs.
The use of AI and its impact on shadow IT
Theartificial intelligence (AI) is also a rapidly growing phenomenon and is among the technologies increasingly being used in an uncontrolled manner within companies. Employees often adopt generative AI tools for tasks such as content creation, data analysis, or project management. While these tools can significantly improve productivity, they do not meet the standards set by CIOs in terms of compliance or internal security policies. For example, sensitive data may be shared with applications AI that do not meet the company’s expectations, paving the way for potential breaches and loss of confidentiality.
For CIOs, the challenge is to monitor the use of these technologies and integrate approved AI solutions that comply with corporate security policies.
The role of CASB in managing employee activities
To manage, supervise, and above all secure, you must first and foremost have visibility. To address this, many companies are turning to solutions that Cloud Access Security Broker (CASB). A CASB is a solution that sits between cloud service users and the providers of those services. It provides complete control and visibility over the use of cloud applications, whether they are authorized by the company or not.
The CASB plays a crucial role in securing shadow IT by providing several essential features. It offers near-total visibility into cloud applications. The CASB enables real-time analysis of employee traffic and uses a SaaS application database that maps domains, IP addresses, and SaaS applications used within the company, whether approved or not. This allows the IT department to better understand the scope of these applications and assess the associated risks.
The key features of the CASB enable:
- Ensure regulatory compliance by monitoring and enforcing policies aligned with standards such as the GDPR, thereby avoiding financial penalties and damage to the company's reputation.
- The integration of access and identity management tools, allowing precise control over who can access which applications and data, while detecting and blocking malicious behavior through real-time monitoring.
- By facilitating cloud governance and reducing the risks associated with shadow IT, CASB enables companies to maintain an optimal balance between employee productivity and IT infrastructure security, while promotingthe innovation andagility required in a constantly evolving technological environment.
Thanks to these capabilities, the CASB has become an essential component of enterprise security. It is part of a more comprehensive approach aimed at addressing all of an organization’s security needs through the SSE (Security Service Edge), which maximizes the scope of threat response by combining SWG, ZTNA, DLP, and CASB functions to provide a comprehensive strategic security solution.
Conclusion
Shadow IT, while it may offer advantages in terms of responsiveness and productivity, poses serious challenges for CIOs in terms of security, compliance, and risk management. In the future, one of the main challenges for CIOs will be to strike a balance between enabling employees to remain productive and ensuring robust IT infrastructure security.
As we have seen, tools such as CASB and increased employee awareness are complementary approaches that help better manage shadow IT while addressing the security, compliance, and efficiency needs of modern businesses.